 System Documentation
System Documentation
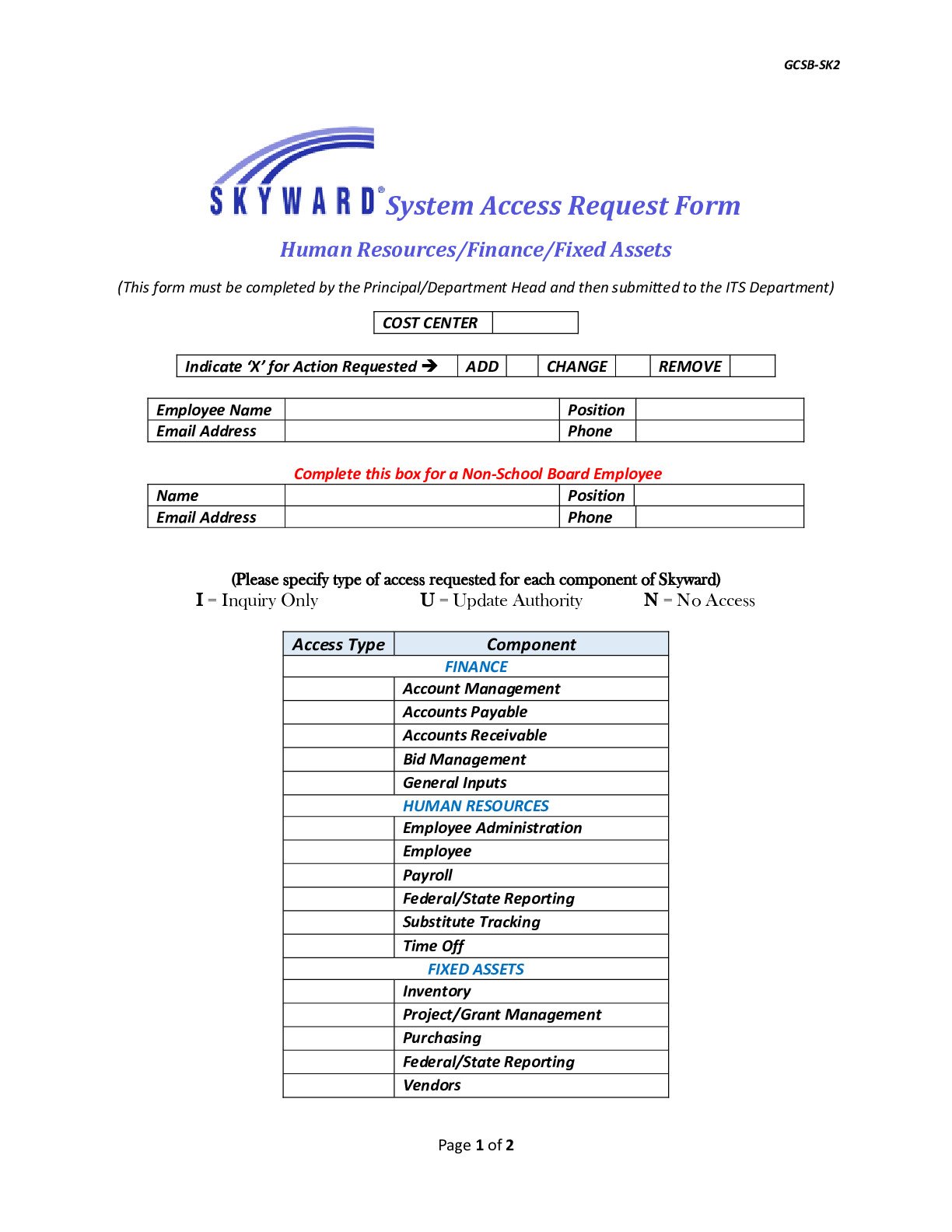
System Access Request Form
Form used by employees to request access to internal systems or software tools.
 Development Guidelines
Development Guidelines
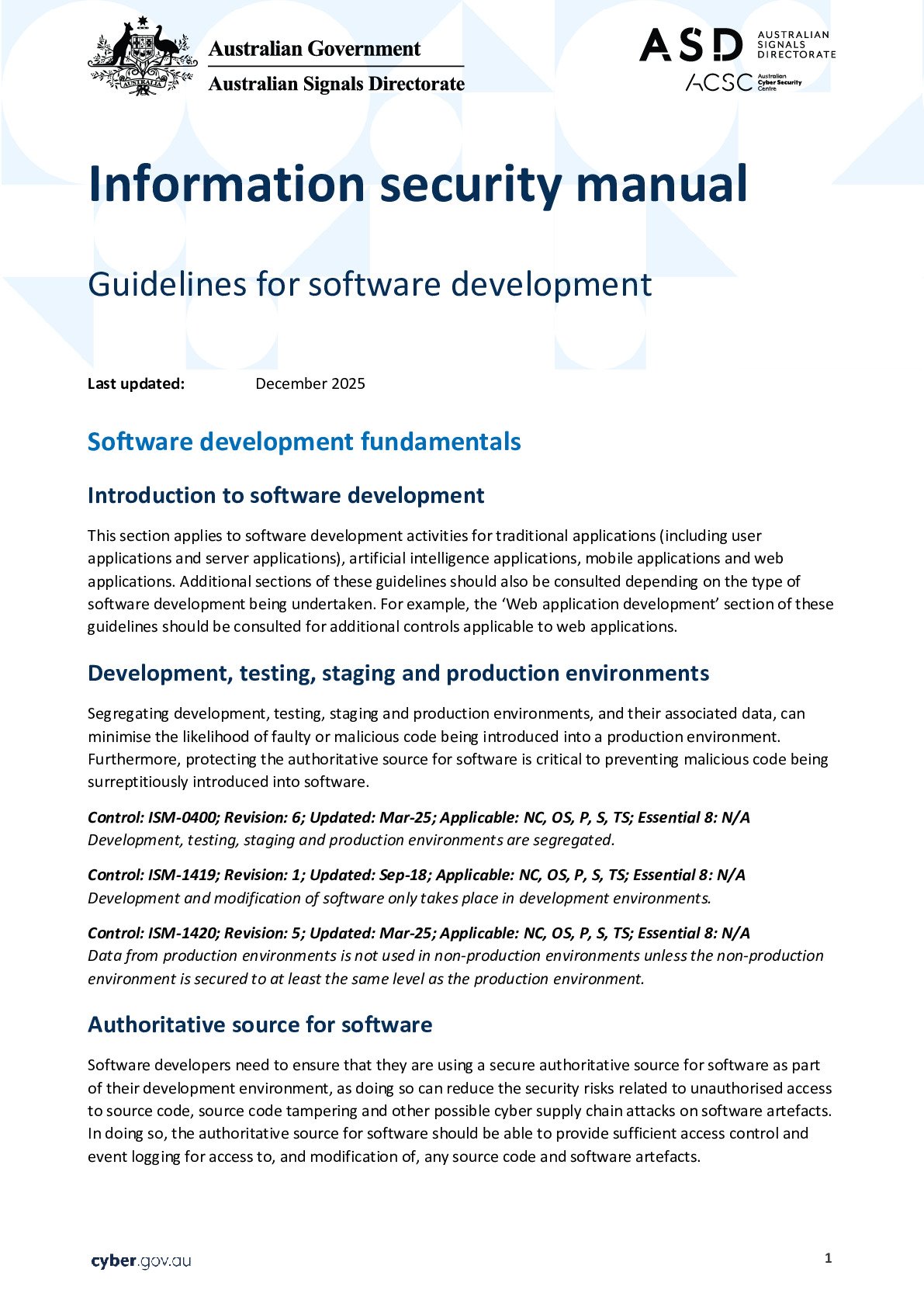
Software Development Guidelines
Coding standards and best practices followed by the development team for building software systems.
 Security Policies
Security Policies
Incident Response Procedure
Steps to follow when responding to cybersecurity incidents or system breaches.
 Security Policies
Security Policies
Data Privacy Policy
Guidelines explaining how company data and customer information must be handled securely.
 Security Policies
Security Policies
IT Security Policy
Document describing security practices including password policies, data protection, and system access.